Rules are sometimes a contentious matter. Whereas some argue they hinder innovation by introducing extreme paperwork, others contend that the absence of clear guidelines can result in unquantified dangers with wide-reaching penalties—from shoppers and organizations to complete markets.
Nonetheless, there are moments when each side of the controversy align—and cybersecurity is a kind of circumstances.
However you could surprise, why cybersecurity? What is going on on this area that creates the required synergies? The reply is that there are two primary drivers for this:
- The rising frequency and class of ransomware assaults have severely impacted organizations, inflicting reputational, monetary, and in some circumstances, human or important infrastructure damages
- Underinvestment in cybersecurity instruments and practitioner abilities
These causes are exactly the place rules play a important function: They intention to deal with these gaps by implementing good safety requirements, imposing penalties for non-compliance, and requiring organizations to allocate assets for prevention, detection, and incident response.
Happily, regulatory our bodies are already appearing. In america, for instance, HIPAA ensures the safety of affected person knowledge inside the healthcare sector, whereas PCI DSS governs the safety of card fee techniques within the industrial area.
Of explicit significance are two main rules rising from the European Union, each designed to considerably enhance cybersecurity resilience and threat administration throughout sectors:
- Digital Operational Resilience Act (DORA)
- Community and Data Safety Directive (NIS2)
Nonetheless, many organizations face vital challenges with regards to implementing these regulatory mandates. Usually, the language utilized in such rules is high-level and lacks prescriptive steerage, making it tough to translate necessities into actionable steps. Moreover, organizations could not have the fitting instruments, processes or infrastructure in place to successfully implement and operationalize these requirements.
This raises a important query: How can organizations obtain compliance in a sensible, scalable method?
NIST Cybersecurity Framework 2.0 to the Rescue
NIST Cybersecurity Framework 2.0 provides invaluable steerage for organizations seeking to handle and mitigate cybersecurity dangers. Whereas it doesn’t prescribe particular options, it offers a strong construction for translating high-level enterprise aims into actionable technical necessities.
Right here is the place you possibly can leverage any cybersecurity instrument utilizing NIST Cybersecurity Framework 2.0 to implement these technical necessities, given the instrument has the required capabilities and functionalities to deal with them.
Enter Cisco Safe Workload.
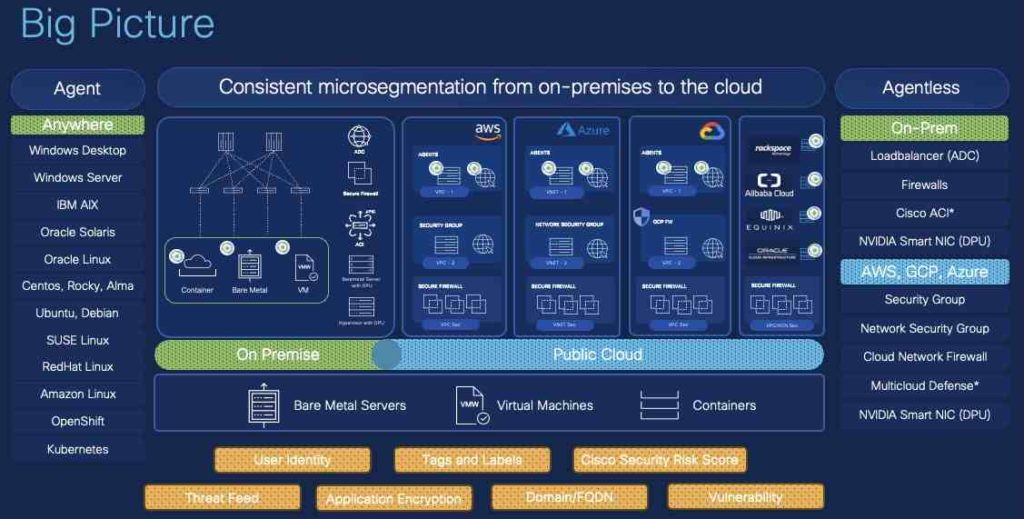
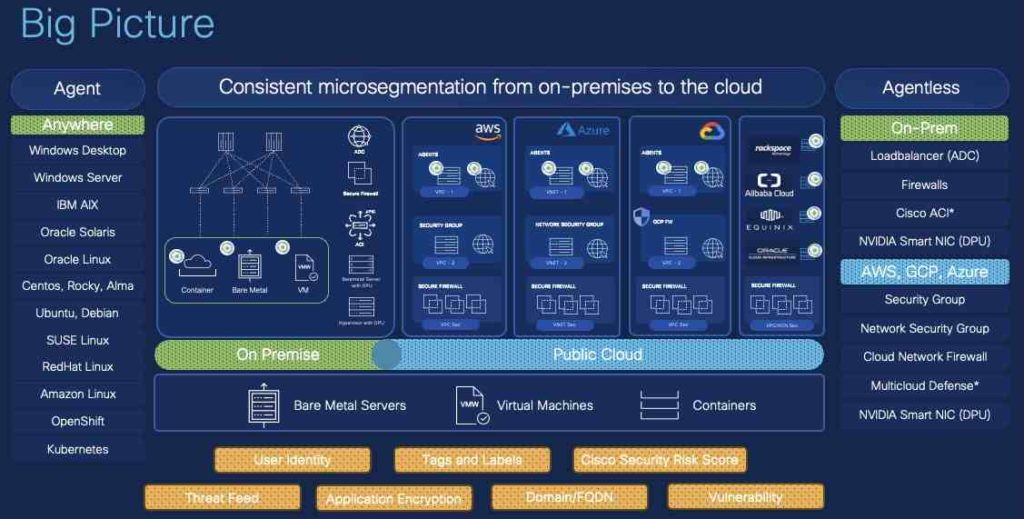
Cisco Safe Workload is a holistic safety resolution designed to ship in-depth utility workload visibility and safety throughout on-premises and multicloud environments. Safe Workload focuses on three primary use circumstances:
- Zero Belief Microsegmentation: Utilizing agent and agentless approaches, Safe Workload can uncover workloads primarily based on labels, mechanically uncover and counsel segmentation insurance policies primarily based on site visitors flows, validate and check the coverage with none operational influence, and implement the dynamic coverage on a number of enforcement factors akin to host-based firewalls, Knowledge Processing Items (DPUs), community firewalls, load balancers, and built-in cloud safety controls.
- Vulnerability Detection and Safety: Using an agent, Safe Workload offers visibility into the applying workload runtime, enabling the detection of susceptible packages and susceptible container pictures. It then leverages this info utilizing vulnerability (Widespread Vulnerabilities and Exposures (CVE) attribute-based insurance policies to quarantine workloads or carry out digital patching by way of Safe Firewall.
- Behavioral Detection and Safety: Safe Workload displays working course of for modifications in habits and an in depth course of tree and course of snapshot. It detects anomalous habits utilizing MITRE ATT&CK or with customized forensic guidelines. By leveraging Safe Firewall’s Fast Risk Containment, safety of each agent and agentless workloads might be achieved.
As you possibly can see, Safe Workload provides the breadth and depth of capabilities wanted to function a core cybersecurity instrument. However the important thing query stays: How can we successfully correlate and map these options to particular technical necessities?
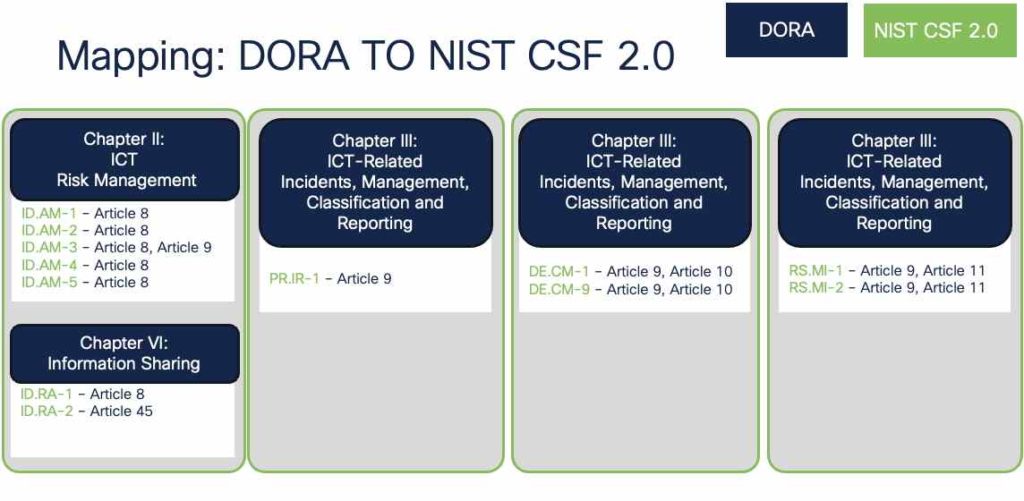
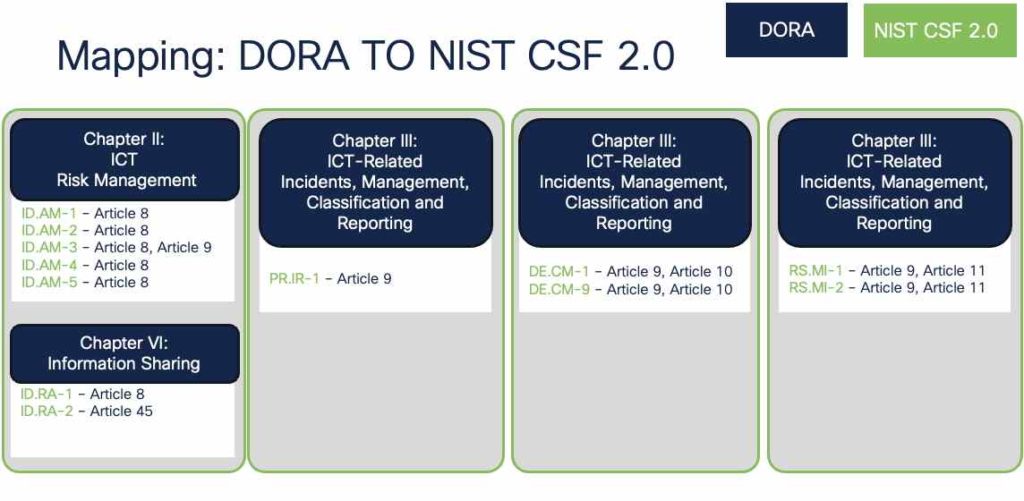
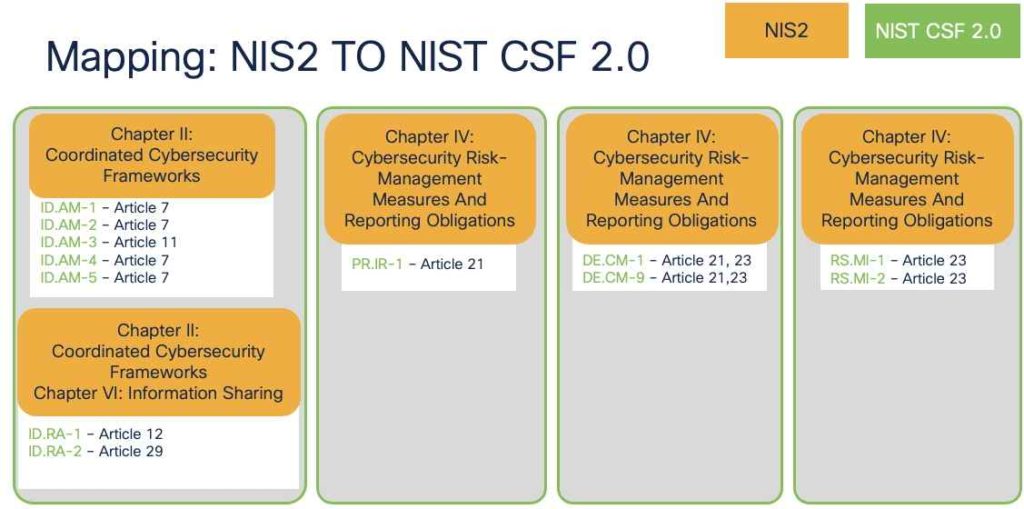
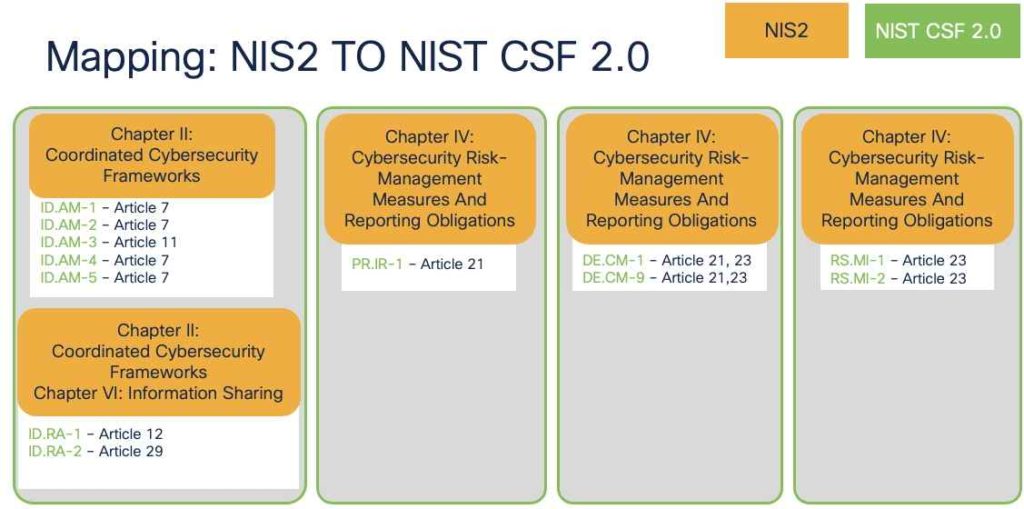
Mapping DORA and NIS2 to NIST Cybersecurity Framework 2.0
DORA and NIS2 necessities are sometimes high-level, requiring IT groups and NetSec groups to interpret and translate them into actionable technical controls for implementation.
To streamline this course of, organizations can leverage NIST Cybersecurity Framework 2.0 as a foundational reference. By mapping its steerage to Safe Workload capabilities, we are able to successfully translate those self same necessities into sensible, tool-driven implementations aligned with DORA and NIS2 mandates.
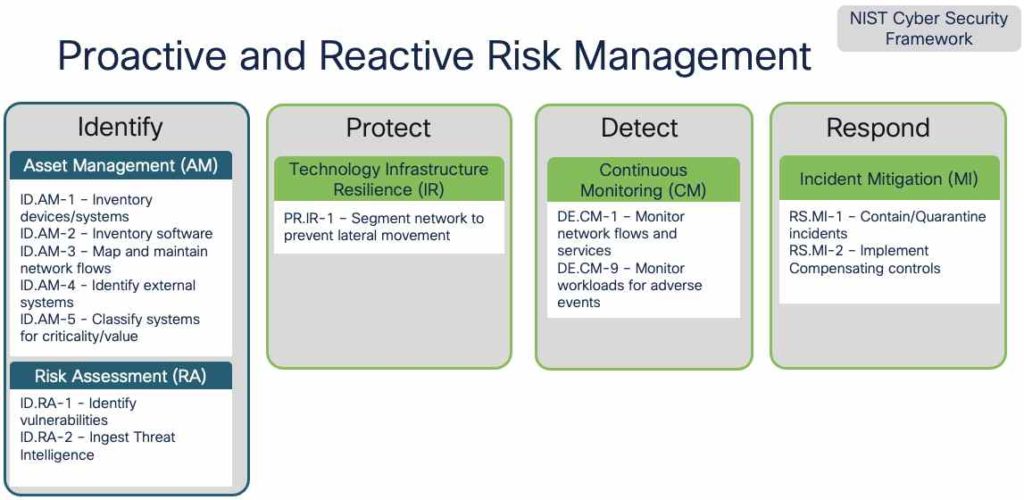
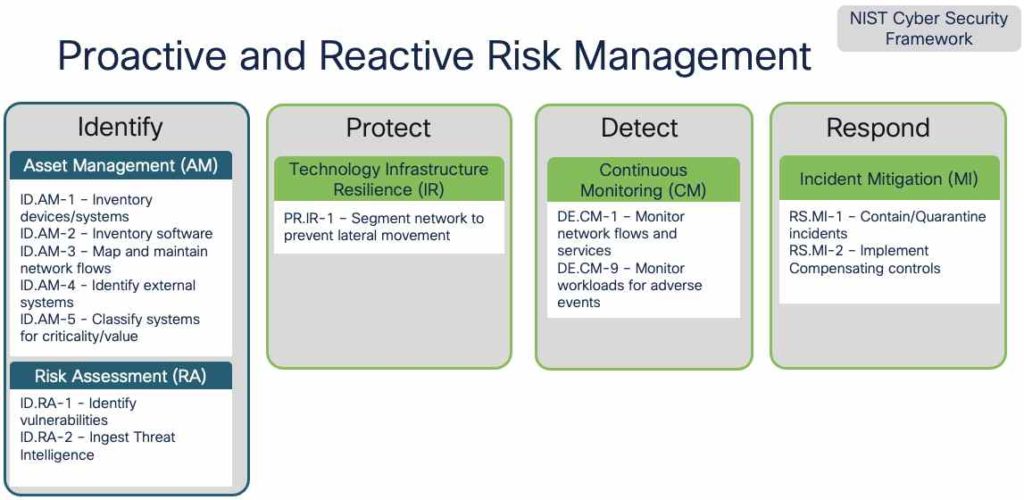
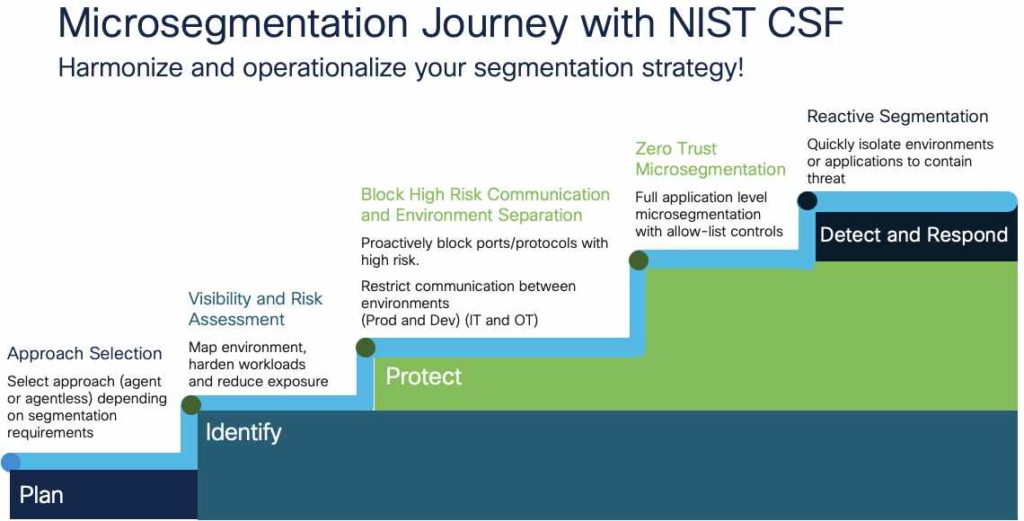
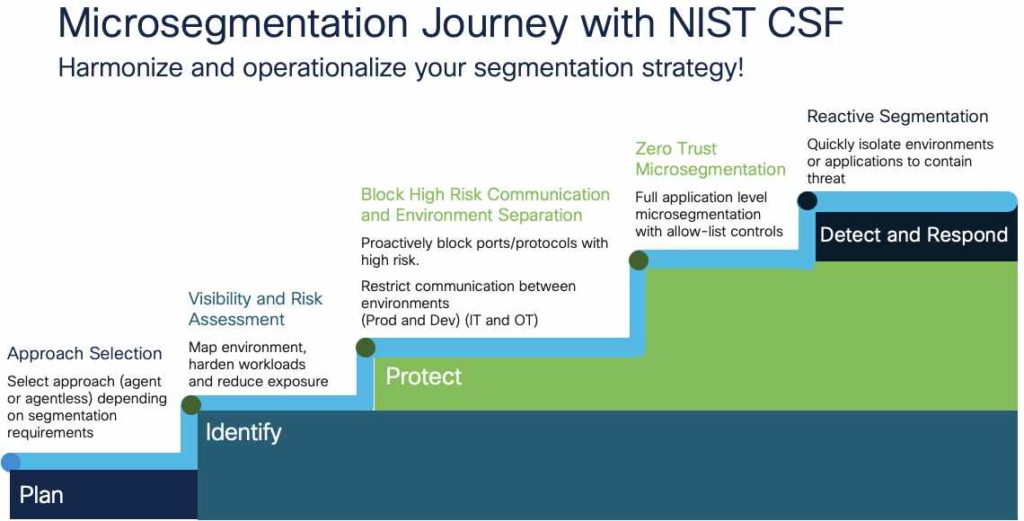
The Microsegmentation Journey With NIST Cybersecurity Framework 2.0 and Safe Workload
Microsegmentation redefines conventional community safety by shifting the perimeter to the person asset. It creates micro-perimeters throughout multi-cloud environments, isolating and securing every workload independently.
This strategy has develop into a sensible basis for implementing zero belief architectures, because it permits the enforcement of least privilege entry on the community stage.
Nonetheless, operationalizing microsegmentation stays a big problem. It requires shut collaboration throughout varied groups—safety, networking, operations, and compliance—which may create complexity and friction. For a deeper dive into these challenges and how one can overcome them, I like to recommend studying the weblog submit “Enterprise Chief’s Information for a Profitable Microsegmentation Undertaking” by my colleague Brijeshkumar Shah.
That is the place Cisco Safe Workload turns into the toolset that may allow organizations to efficiently implement microsegmentation, whereas additionally supporting compliance efforts. By fostering collaboration throughout groups and integrating with current processes, Safe Workload helps make zero belief achievable and scalable.
Navigating Compliance with the Proper Method and Instruments
Regulatory and compliance mandates might be complicated and difficult to navigate. Nonetheless, with the fitting strategy—translating enterprise necessities into actionable technical controls—and the fitting toolset to implement them, the trail to attaining compliance turns into much more manageable. To see how Cisco Safe Workload can help your compliance journey, take a look at my Cisco Stay session, the place I showcase reside demos and sensible examples of how this resolution might be utilized to satisfy regulatory necessities successfully.
Wish to be taught extra? Take a look at the Cisco Safe Workload product web page.
We’d love to listen to what you suppose! Ask a query and keep linked with Cisco Safety on social media.
Cisco Safety Social Media
Share:

